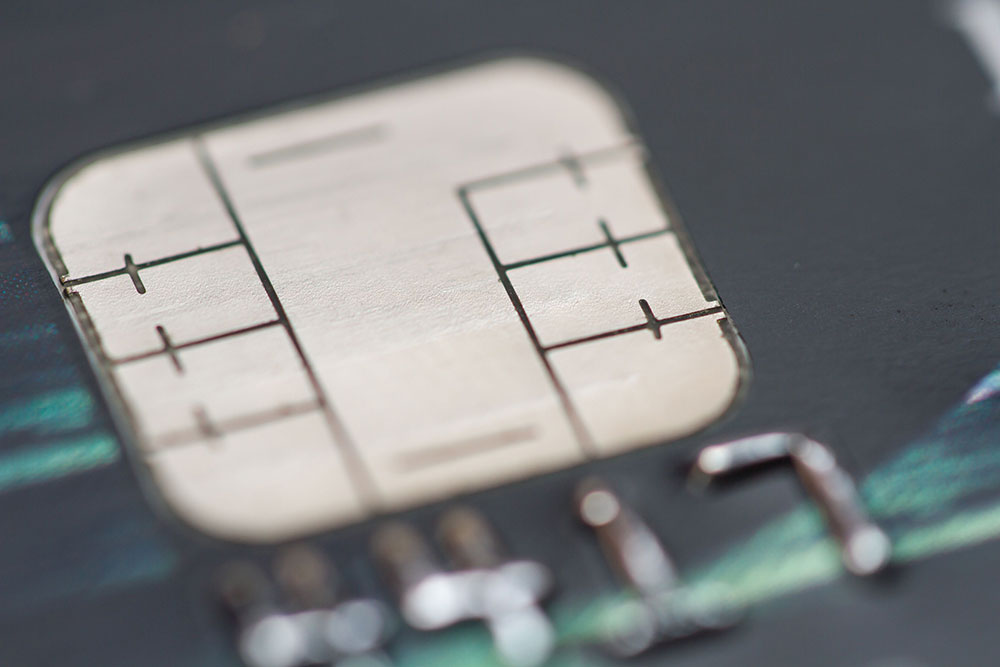
Until last October, the United States was the last developed country without EMV. Since then, many Americans have started getting used to their new embedded-chip payment cards.
EMV has been tremendously successful in preventing fraud internationally, so this switchover to EMV chip cards doesn’t just bring the United States in line with pretty much the rest of the world; it is also expected to reduce the increasing amount of payment card fraud.
The little chip on the front of your payment cards does have its limits. Wherever EMV has been implemented abroad using the chip-and-PIN version, fraud has been significantly reduced and sustained. Unfortunately, that is not the way American EMV cards are made to function, at least for now.
An article on the Access Payment Systems blog states that, according to the National Retail Federation, the reason the EMV chip-and-signature cards are not as effective as the chip-and-PIN cards is because they lack the additional requirement for a PIN number.
That is not to say chip-and-signature EMV cards are not effective. Quite the contrary. For card-present transactions (those in which the consumer has the actual payment card in-hand), all chip cards are more secure than regular magnetic stripe cards.
When a merchant has an EMV-ready terminal, a chip-and-signature card transaction is just about as safe as a chip-and-PIN one, especially regarding data breaches like the Target and Home Depot ones from a couple of years ago. This is because a dynamic transaction code– a code that can only be used for that specific transaction – is created each time it’s used, preventing hackers from cloning the data.
The chip-and-signature card’s vulnerability lies in the magnetic stripe, which still contains the cardholder data that is attractive to hackers – the data is static, meaning it always stays the same, making it susceptible to being skimmed and cloned, then used for fraudulent purchases. An EMV card does not have the magnetic stripe, just the chip that helps to prevent hackers from cloning the data, since it contains a dynamic code, making it basically useless for any other transaction.
For card-not-present (CNP) transactions, it is a completely different story. Ecommerce purchases made over the internet or phone require manually entering secure information. Unfortunately the potential for fraud is higher in this case, because there really is no way for the consumer to prove he or she is the owner of the card. Some sites have “safeguards” like entering the CVV or security code (the three- or four-digit number that is usually on the back of the card) or answering security questions, but an article on the Rippleshot blog states that “in every country that has adopted EMV, card not present fraud has increased substantially. In the UK specifically, card not present fraud increased for four straight years after EMV was implemented, and is still at higher levels than it was pre-EMV.”
Full EMV adoption in the United States is still several years away, so chip cards will continue to be issued with magnetic stripes, which means that the potential for card data and consumer information to be stolen and cloned will be with us for a while. The best way for consumers to protect themselves is to use the EMV feature on payment terminals when it is available and to avoid using payment cards at businesses that are most susceptible to skimming, like gas stations.